Description
Python Hacking Course Real Ethical Hacking with Python PYCEH23+. Python hacking course Real Ethical Hacking with Python PYCEH23+. Are you ready to unlock Python’s full potential and become a skilled ethical hacker? Look no further than “Ethical Python Hacking: Mastering the Art of Cyber Security”. This comprehensive and comprehensive course is designed to equip you with the knowledge and practical skills necessary to excel in the exciting world of ethical hacking. With a focus on practical applications, this course covers everything you need to know about Python programming, making it accessible to both beginners and experienced programmers. You will embark on an exciting journey where you will learn how to harness the power of Python to manipulate MAC addresses, develop network scanners, perform Man-in-the-Middle attacks, intercept network traffic, create your own pentesting RAT (Remote ) use. access to Trojans) malware, and much more. This course begins with a solid foundation in Python fundamentals. Even if you’re new to programming, you’ll quickly grasp the key concepts and techniques essential to ethical hacking. From there, you’ll move into the world of network security and learn how to manipulate MAC addresses using the terminal, as well as develop your own Python program to dynamically change MAC addresses. This skill is invaluable for hiding your identity and increasing your hacking capabilities. Next, you’ll explore the intricacies of ARP (Address Resolution Protocol) and the ARP table. You’ll gain a deep understanding of how these protocols work and their vulnerabilities, and then apply your knowledge to create a network scanner from scratch. By the end of this section, you will be able to effectively discover vulnerable devices on a network, an important skill for any ethical hacker. One of the most powerful techniques in the arsenal of ethical hackers is the Man-in-the-Middle (MiTM) attack. In this course, you will not only understand how these attacks work in reality, but also program and run your own MiTM application using Python. You’ll learn how to fake routers and targets simultaneously, and fix any problems you encounter along the way. This knowledge allows you to intercept network traffic and exploit login credentials from devices on the same network, uncover critical information, and strengthen your cybersecurity defenses. As you take your skills to the next level, you’ll create your own intrusive RAT malware. A remote access trojan (RAT) provides unauthorized access to a target system and allows you to explore and control it remotely. You will develop a powerful RAT malware from scratch with client and server components and run it on both Windows and Kali Linux platforms. By understanding the inner workings of such malware, you will be better equipped to defend against it. Understanding sockets and their functionality in Python is very important for remote access and control. In this course, you will explore the intricacies of sockets and how client and server applications communicate. You will create a client-side application and establish remote access connections, which will allow you to effectively explore and control remote systems. Finally, you will explore server-side implementations of remote access techniques. You will dissect each line of code and understand its importance in creating a secure and robust connection between client and server. This knowledge enables you to develop secure remote access solutions and protect against unauthorized access.
What is in the Python Hacking course | Real Ethical Hacking with Python You will learn PYCEH23+
-
Basic syntax and structure of Python.
-
How to work with variables and data types
-
How to use operators for mathematical and logical operations
-
Control structures such as if-else statements and loops.
-
How to write and call functions in Python
-
How to manipulate strings and work with string methods.
-
How to manage user input and output data
-
Lists and their operations, including indexing and pruning.
-
Tuples and their immutability in Python
-
Dictionaries and their key-value pair structure.
-
File management and reading from/writing to files.
-
Exception handling to handle errors in your code.
-
How to work with modules and import external code
-
Understanding and using libraries in Python
-
Regular expressions for pattern matching and data validation.
-
Encapsulation, inheritance and polymorphism in OOP
-
How to manage date and time in Python
-
Working with sets and performing set operations.
-
Comprehension lists for concise and efficient code.
-
Understanding and using generators and iterators.
-
An introduction to recursive and recursive functions.
-
How to install and work with third-party packages using pip.
-
Best practices and coding conventions for writing clean and readable code.
This course is suitable for people who
- Beginner programmers who want to enter the field of ethical hacking and learn how to develop hacking tools using Python.
- Cyber security enthusiasts who want to expand their knowledge and skills in ethical hacking and penetration testing.
- IT professionals or system administrators who want to understand hacking techniques and develop defense strategies.
- Cybersecurity students or researchers who want to gain hands-on experience in developing hacking tools.
- Professionals involved in software development or network administration who want to increase their understanding of security vulnerabilities and develop tools to test and secure their systems.
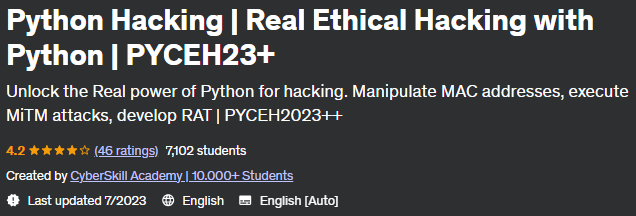
Details of the Python Hacking course Real Ethical Hacking with Python PYCEH23+
Headlines of the Python Hacking course Real Ethical Hacking with Python PYCEH23+ on 7/2023
Python Hacking course prerequisites Real Ethical Hacking with Python PYCEH23+
No programming experience needed, you’ll learn everything here
Course images
Sample video of the course
Installation guide
After Extract, view with your favorite Player.
English subtitle
Quality: 720p
download link
File(s) password: www.downloadly.ir
Size
2.3 GB